February 30, 2023 The cryptocurrency winter continues to wear us down inertia which seems almost unchangeable. the bitcoin Keep wandering $18,000, and even the bad news seems to have stopped raining. However, tonightOn-chain data inspectors noticed an event that was more expected. Satoshi Nakamoto He transferred his millions of bitcoins to another wallet. Death Note for Bitcoin?
Scenario of the apocalyptic end of the world or the return of the prodigal son?
This is a widely discussed and debated scenario in the field of cryptography. What would happen if we noticed a movement on a portfolio? Satoshi Nakamoto ?
One can easily imagine the wave of panic that would accompany this discovery. Some may think of hidden message To announce the failure of his invention. Others may rationalize the situation by convincing themselves of it Move does not sell.
What if the reality was completely different? And if this treasure of about $20 billion Currently a specific job for Security like bitcoin ? This topic will be the purpose ofSeries of articles which I will share with you Encryption date. How could this be upset if, one day, one of Millennium math problemswas to be resolved?
Good reason to understand all the cogs and fundamentals of coding at its core bitcoin. Better late than never!
electronic signature
Secure authentication
Before talking about the blockchain, electronic signature It is the first building block of our beloved cryptocurrency. One of the primary components of its encryption mechanisms. A decentralized on-chain electronic ledger, which enables the exchange of digital assets by being able to track all transactions made. That’s what bitcoin. But why are they necessary?
Let’s take as an example your connection to FB. What happens if the login request includes your username and password? clearly ? A hacker may interfere when a file is being sent data To the server, pretending to be Facebook to the latter and I stole them. Even encryption doesn’t seem to be enough. Because this hacker can directly transmit encrypted identifiers to connect on your behalf.
So how can you be sure that you are communicating well with FB ? This is where the file is needed letter signatureis necessary for any type authentication Believe on the web. Whether it’s to sign a document, or connect to your favorite social network. Authentication, sometimes without having to reveal the password or private key. But how does it work?
The five components of a secure signature
Before answering this question, let’s take a look at Properties which the signature must meet to allow you to be authenticated by example Our handwritten signatures :
- authenticity : signature must make it possible to find identification or site alias. It’s not very obvious when you look at the scribbles we use to sign our bank checks.
- Obvious tampering : The signature must prove that you are the only one who can provide it and that he cannot come of a rapist. He missed our parents’ hand-signatures, which were successfully transcribed into our correspondence books during our younger years in college.
- Not reuse : signature must be Unique and relatable With every signed document. Perhaps the only property to which the handwritten signature responds strongly enough.
- Not to change : When the document is signed, it must become immutable to avoid any document they change which you will not agree to. This is why we avoid signing a blank check. You will not be able to dispute the written amount after that.
- Irreversible : Finally, the signature must be irrevocable. If it satisfies all of the above characteristics, then it is necessarily signed Author From him and he should not be able Langerhans. This can quickly cause problems when a handwritten signature or a paper document is immutable.
So the security of handwritten signatures is very imperfect. On the other hand, these properties are imperative for such protocols bitcoin.
Back to typical of FBIn order to allow your connection in a secure manner, the platform must authenticate the server to ensure that it is not a hacker trying to usurp your identity. to do this, Asymmetric encryption protocol It is used, just as when signing transactions on the blockchain. Once authenticated, Facebook and the server will exchange data by Symmetric encryptionbecause it is simpler and less resource consuming.
The functioning of an electronic signature is intrinsically related to the chosen encryption protocol.
The two main types of encryption
Symmetric encryption
exist who are they The main types of encryption. theIt has symmetric encryption, where you and your interlocutor have one key to encrypt and decrypt your exchanges. And Asymmetric encryption Where you have two keys, one public and one private.
To explain how symmetric encryption works, let’s take a simple example:
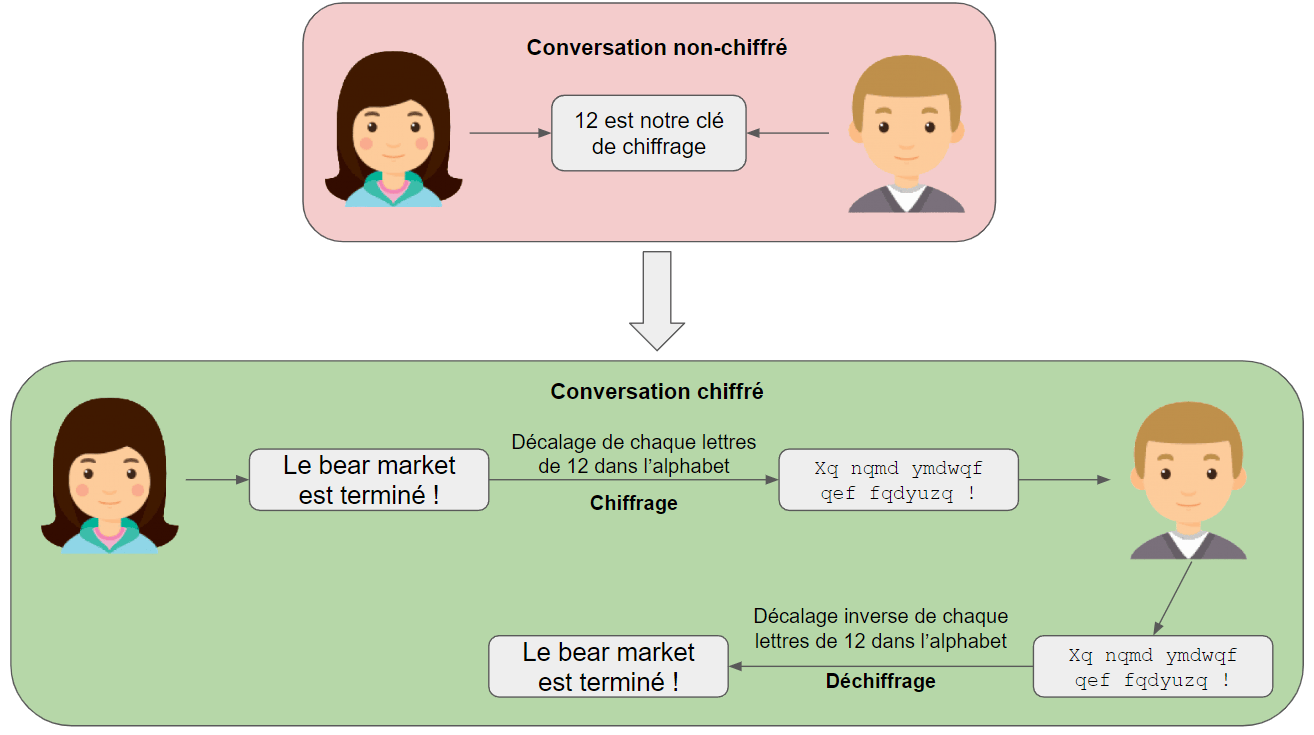
to communicate secretly, Alice And Bob We agree on a number, at random, 12. In order to send each other a message, they will the blade By shifting each of their letters in the alphabet by 12 rows. the message to me will become Mthe message B will become Not, etc. When they receive a message, they just have to change all the letters of the message back opposite direction to restore its original meaning. Not very strong, you will agree. But other systems are possible. For example, a mathematical sequence that would change the encryption key with each letter of the message.
But symmetric encryption has it disadvantage. to be able to speak secretly, Alice and Bob You must agree in advance on the encryption key to be used. But this agreement is not encrypted and cannot be completely confidential. So it seems impossible to speak in secret without speaking unconfidentially beforehand. Even invention Diffie-Hellman key exchange Which will lead to the emergence of asymmetric encryption.
>> Do you prefer to keep your cryptocurrency safe? Choose ledger wallet (trade link)
Diffie-Hellman key exchange and asymmetric encryption
This mechanism was first thought of by programmers Whitfield Davy And Martin Hellman in 1976. Two interlocutors who have never communicated before are allowed to secretly exchange an encryption key that will be used during their future conversations.
This system is based on the use of the so-called One-way mathematical function. It works so that the result of this function applied to a number Easily calculated. On the contrary, the reverse path, i.e. finding the prime number starting from the result, is a very complex arithmetic operation and No way in a humanly reasonable time. This is called computational security The Diffie-Hellman decision hypothesis. Even if the encryption function becomes public, don’t worry, the message will remain hard to understand.
Let’s go back to the two interlocutors Alice And Bob :
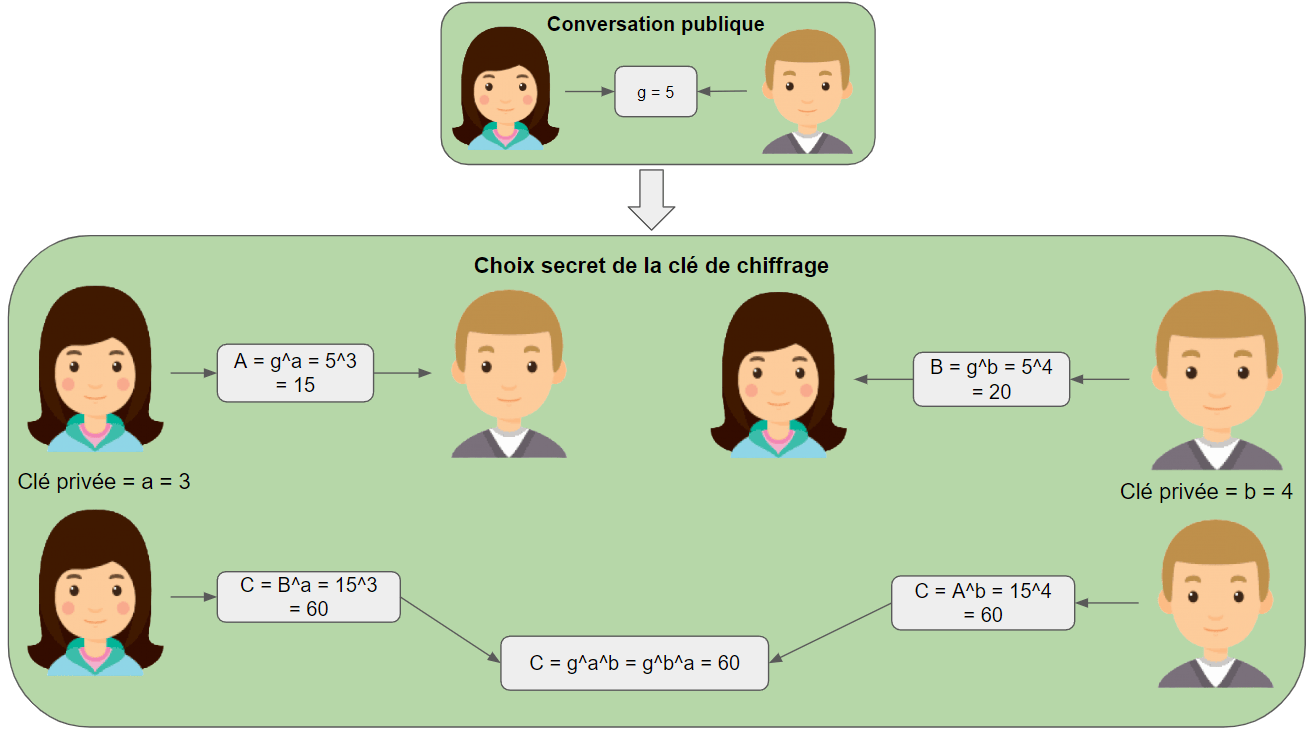
Alice And Bob He will choose in an undisclosed way the number that will act as public keyLet’s call it g And each secret keyrespectively, to me And B. in order to agree on Symmetric encryption key For their future conversations, named againstThey will perform the following calculations:
- Alice Calculation procedure a = g ^ a And send the result to me to me Bob.
- Bob Calculation procedure b = g ^ b And send the result B to me Alice.
- Alice receives the number B Then do the calculation c = b ^ a = (g ^ b) ^ a.
- Bob receives the number to me And we do the math C = A^b = (g^a)^b.
If you haven’t forgotten your college math classes, you will have noticed that the calculations g ^ b ^ a And g ^ a ^ b lead to the same result! Alice And Bob So I found a shared secret key to do the symmetric encryption without Start replace it and without anyone being able to calculate it… as long as its private key, the rest !
function as energy Unidirectional function. If a third person has access to all exchanges between Alice And Bob And know the numbers gAnd to me And Bthe latter will not be able to find the private keys to me And B So is the end result against.
To ensure that performing these calculations in the reverse path is impossible, to me And B Should be in very large numbers. For crypto fans, I deliberately obscure the part Normative mathematics. It is used to simplify accountsAlice Based on Bob (And so that neither of them can calculate the private key of his comrade) so that no one gets drowned. Just understand that it is Math trick Which makes it possible to realize the colossal powers of numbers very easily. Even the greatest calculators in the world wouldn’t be able to calculate for example 6^3000. If you want to understand more in-depth, I suggest you wait for my next article!
Diffie-Hellman key exchange So it brings a whole new way of looking at cryptocurrencies. Extension is allowed Total End-to-end plus robustness far exceeds what our most powerful computers can compute as long as users’ private keys are large enough numbers. Big. However, the latter does not yet meet all the conditions that must be met in an electronic signature. We just touch the asymmetric Bitcoin crypto with our fingertips. Moving on, we’ll look at encryption RSA To finally deal with the cryptography that Bitcoin uses, that is cryptography ECDSA.
But how could the great principles of cryptography and the security they imply lead to the “death of Bitcoin”? Save this for my next articles, you will have to arm yourself with patience and come back next week !
In cryptography, don’t skimp on caution! Therefore, to keep your crypto assets safe, the best solution remains a personal hardware wallet. in LedgerThere is something for all profiles and all cryptocurrencies. Don’t wait to put your capital in safe (trade link)!

Commentaires
Enregistrer un commentaire